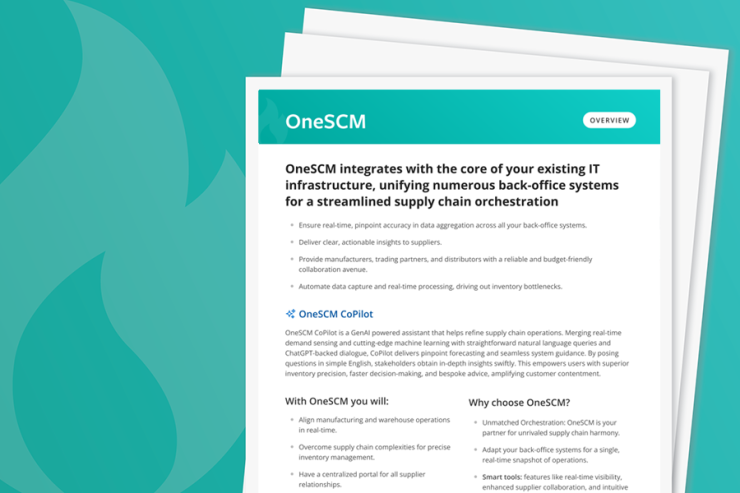
OneSCM's supply chain orchestration delivers aggregated and completely accurate data in real time across your many back-office systems. This simplifies the distribution of actionable intelligence to suppliers while providing manufacturers, trading partners and distributors with a reliable and low-cost way to collaborate.
Why OneSCM?
You need to keep your manufacturing and warehouse operations in sync in real time.
But supply chain complexity often makes it difficult for businesses to employ accurate means for monitoring their inventory. In fact, inventory visibility is one of the top issues keeping supply chain leaders up at night.
By automating data capture and real-time processing across your manufacturing and distribution environments, you can eliminate inventory bottlenecks at the core of your business processes.
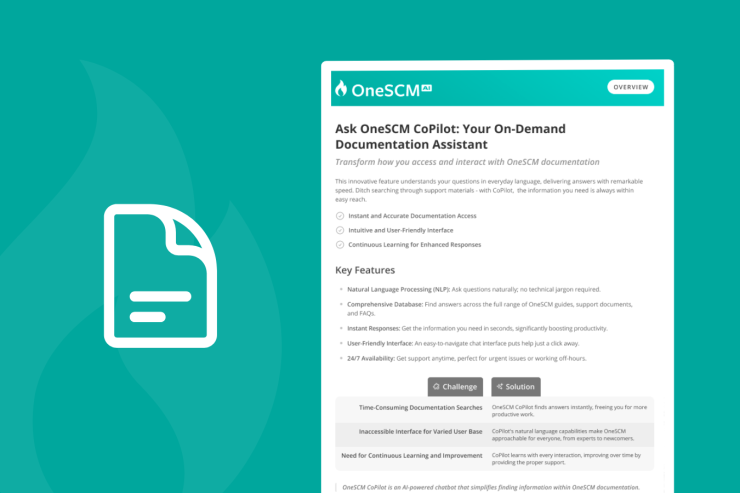
ASK ONESCM COPILOT: YOUR ON-DEMAND DOCUMENTATION ASSISTANT
Transform how you access and interact with OneSCM documentation. This innovative feature understands your questions in everyday language, delivering answers with remarkable speed. Ditch searching through support materials - with CoPilot, the information you need is always within easy reach.

THE TOOLS YOU NEED
- Manage all supplier relationships through a single portal
Recover valuable time and IT resources that are currently being wasted by managing individual B2B supplier connections and system profile mappings via the ERP and other disparate data systems.
- Increase collaboration with suppliers
With just one shared portal to log into, you will enjoy more frequent and quality interactions with suppliers of varying volume, technology and integration levels — enabling a more coordinated planning and execution strategy.
- See and manage your entire global supply network
With access to every communication, transaction and supplier record consolidated in one place on any device, you can confidently deal with urgent issues in real time as well as measure and improve the performance of your entire supply chain.
- Automate workflows and communications
From purchasing to payment , achieve a more efficient manage-by-exception environment.
- Eliminate manual data entry
Prevent data duplications and the possibility of mismatched/out-of-sync data — across every business function.
COMPLEMENTARY IGNITETECH UNLIMITED SOLUTIONS
Check out the solutions below, available free as part of your OneSCM subscription:
AlertFind
AlertFind
Enterprise notifications to communicate important information, monitor responses and verify staff safety.
Blog Posts

Apr 17, 2024
IgniteTech Integrates AI Features Across Its Enterprise Software Portfolio
IgniteTech delivers AI-powered enhancements for 12 of its leading software products, available now…
Apr 11, 2024
Supercharge Your Team: Expert Knowledge on Demand with Jive Personas
Discover how Jive Personas, an innovative AI-driven solution, transforms the way organizations…

Apr 8, 2024
How computers understand Human Language
Unravel the mysteries of how computers understand human language through the fascinating world of…

Oct 21, 2020
Announcing IgniteTech Insights, our New ML/AI Offering
New capabilities advance mission-critical Expert System processes

Apr 10, 2019
How Unseen Costs Are Hurting Your Business's Bottom Line
To maintain healthy bottom lines, organizations should consider their options for identifying and…

Jan 4, 2019
Why You Need to Switch to Time-Driven Activity-Based Costing Now
If you haven’t already made the switch to a time-driven ABC model, here’s why you shouldn’t wait any…